Today we will have a look at the different approaches which can be taken to validate XSS. There is a game by google which can help us in understanding this. The game has 6 levels, each one different from the other. The headings are hyperlinked. feel free to play it ..enoy. Let’s crack the code below.
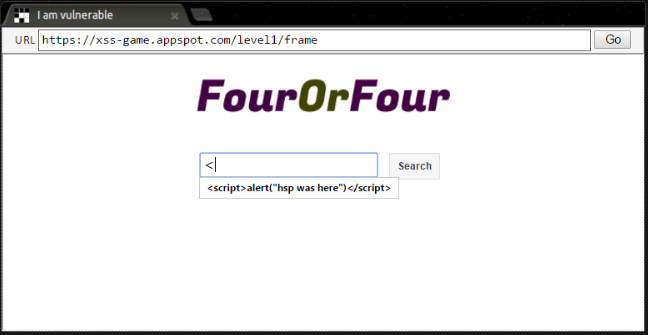
Level 1 – Hello, world of XSS
This one is straight forward : Script tags will do the job
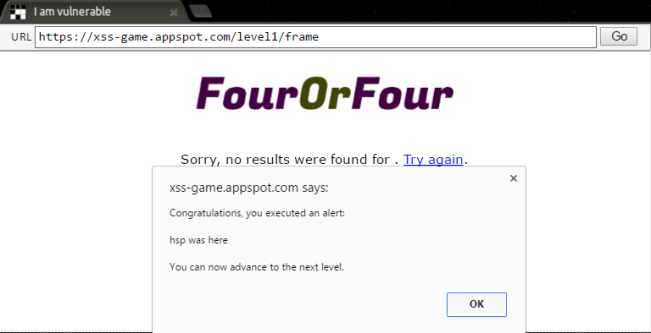
Level 2 – Persistence is key
This one is an example of Stored XSS. Script tags may not work everywhere, Image tags may work.

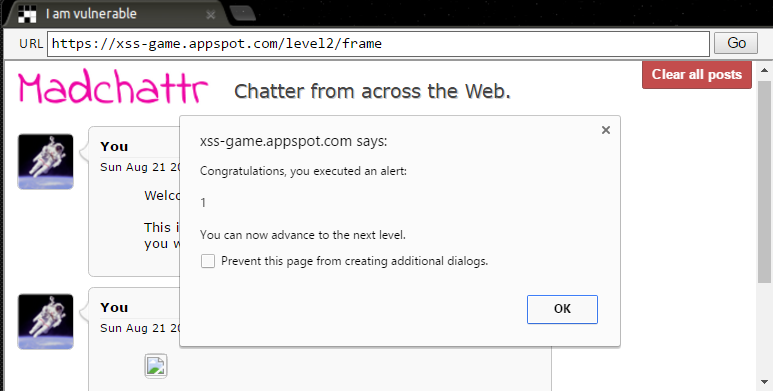
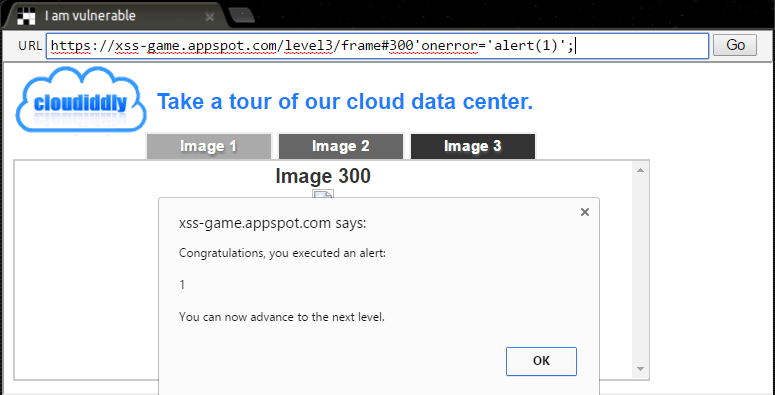
Level 3 – That sinking feeling…
It is noticeable that frame no changes as we click on diff images. Lets see how the error is handled in case we enter a frame no manually which does not exists.
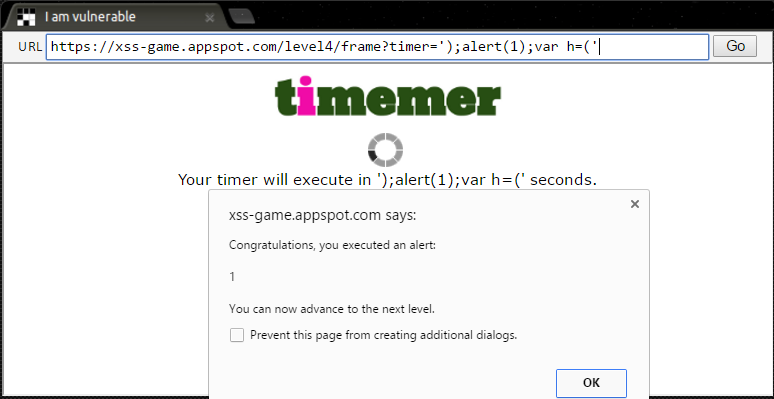
Level 4 – Context matters
A tough one.
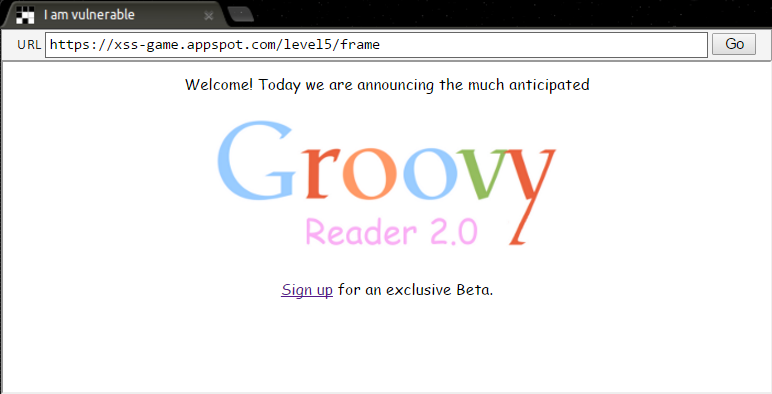
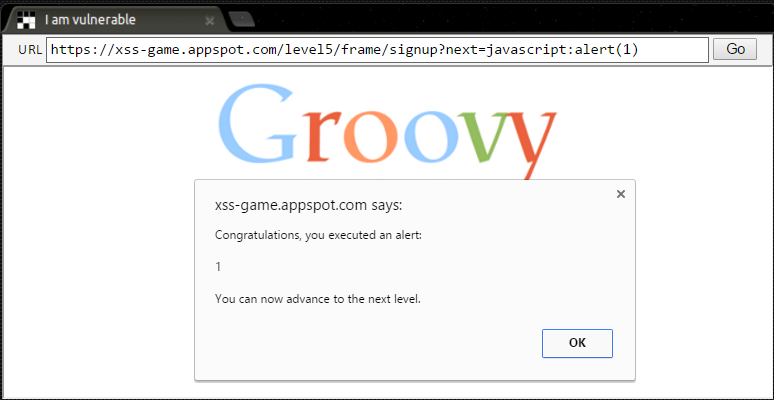
Level 5 – Breaking protocol
Here we can see that once sign up is clicked, URL changes and we have next=confirm.
We altered the URL as below. Now even if you hit go without entering the email, the url will remain same.
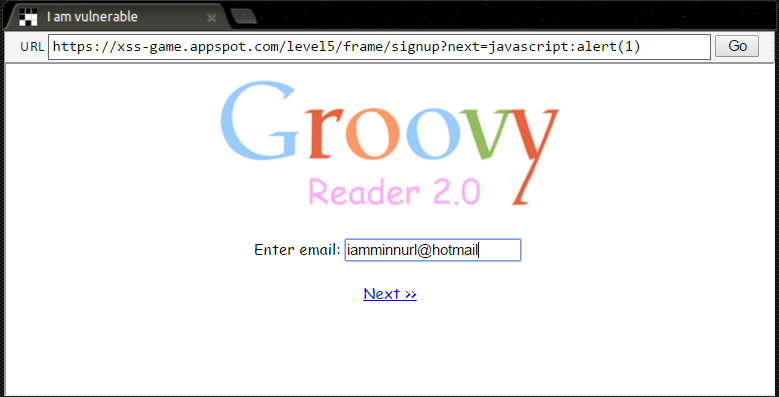
Now enter the mail and hot next.
Level 6 – Follow the 🐇
Gadget being fetched from /static

Lets see if we can change that and refresh.
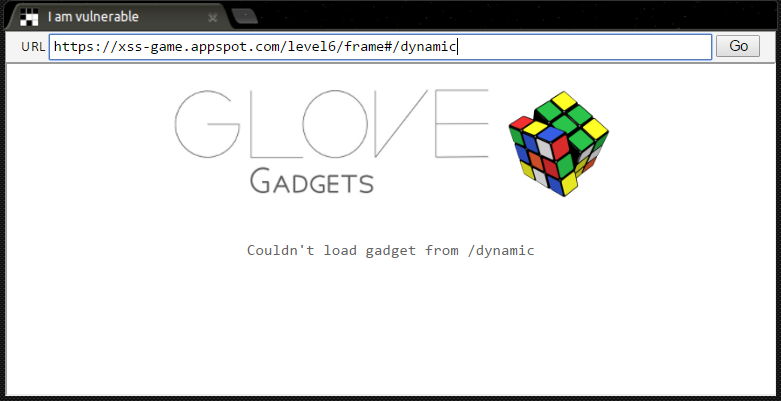
This level can be passed in 2 ways. Refer to a JS object from some other source.Second way is as below.

DESSERT TIME

